“Dear David, I trust as Mr. Joseph trusts you and It is because Joseph is trusted by the trust-worthy gentleman Mr. Adam.”— When it comes to the SSL based security, this is how a chain of trust is formed and a certificate issued to a server A is trusted because the chain of trust (SSL Certificate Chain) reaches to a Root Certificate Authority (Root CA) through multiple layers of intermediate CAs.
In this article, I will explain about Certificate Chaining (Chain of trust) and will explain basic terms and concepts about CA (Certificate Authority), Root Certificate, Intermediate Certificates, Leaf Certificate (Server Certificate) and how a SSL Certificate chain works to establish a secure connection which is trusted by the client.
SSL Certificate Basic Concepts: Introduction to CA (Certificate Authority)
In order to build a relationship of trust between a client and sender for digital communication over the internet, SSL/TLS certificates are used. For this SSL based secure communication, either One Way SSL is used or else in a typical B2B scenarios, Two way SSL (Mutual SSL) approach is used. You can refer to another article I wrote explaining One Way SSL and Two Way SSL in detail.
In either case, certificate based communication starts through a handshake mechanism which works on the principles of mutual trust. This trust is rooted at the top level with a root CA who is a certified, highly regulated authority which is trusted and authorized to issue and sign digital certificates.
There are multiple layers of CA with top-most Certificate Authority known as Root CA which is the most trusted body which can issue Root Certificates and is considered as the primary authority to be trusted. Under Root CA, there can be n number of Intermediate CAs which are themselves trusted by Root CA and are eligible and authorized to issue certificates.
Typically, your web browsers store Root CAs certificates in the trust store and whenever any secure website is accessed, SSL handshake mechanism works by utilizing this trust store to validate any subsequent intermediate or leaf certificates.
SSL Certificate Basic Concepts: Intermediate Certificates and Leaf (Server) Certificates Explained
In a typical scenario, SSL certificate that is issued to a server from a CA is a bundle or a chain of certificates (chain of trust) with Root CA certificate, intermediate certificates and a Leaf Certificate. Intermediate certificates belong to any intermediate CAs who are involved in issuance of the certificate.
A Server Certificate which is also known as Leaf Certificate or user certificate is the SSL/TLS certificate which is issued to the user by the Certificate Authority (often by an intermediate CA). A leaf certificate is bundled with intermediate and Root CA certificates and only then chain of trust can be validated for SSL handshake.
SSL Certificate Chaining: How Chain of Trust Works for SSL/TLS Certificates
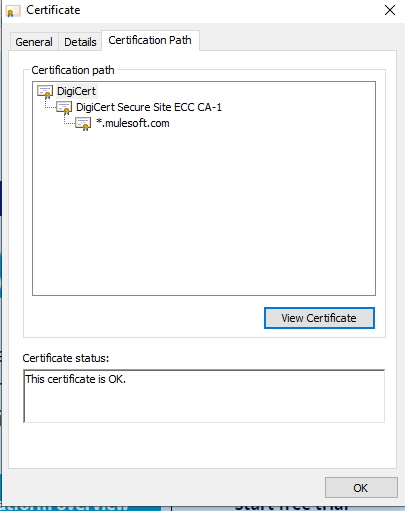
Now that we have explained all the basic concepts associated with SSL certificates and SSL/TLS certificate chaining, let’s wrap up the concepts by explaining with an example, how SSL chaining works in order to build a relationship of trust and how Server Certificate, intermediate certificates and Root Certificate build a hierarchy of trust.
Let’s suppose that we want to access https://mulesoft.com through a secure SSL/TLS connection. For this, you will access this URL from your browser with the aim of having one-way SSL based secure communication between your browser and MuleSoft server. You will trust the site only if certificate that is provided by MuleSoft website to your browser is trust-worthy. This trust will be guaranteed if the server certificate of MuleSoft is issued by a trust Root CA or by any intermediate CA who is trusted by a Root CA. Trusted Root CAs will be already available in your trust store and your browser will check the trust store for this purpose.
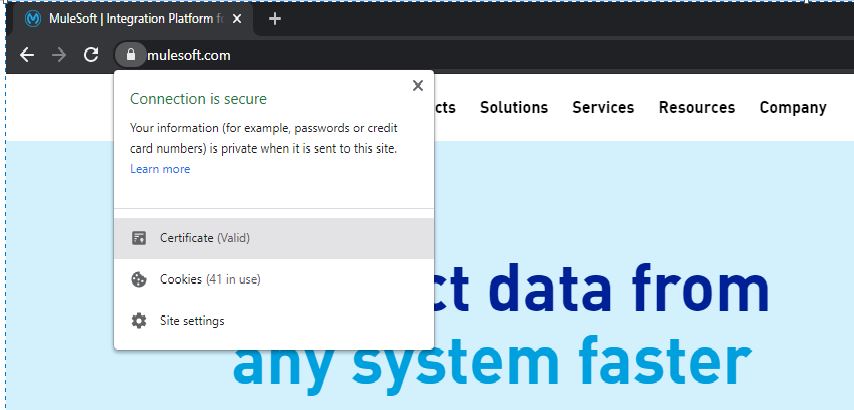
As you can see below, when we tried to access MuleSoft official site, our browser trusted the server by stating its certificate as valid.
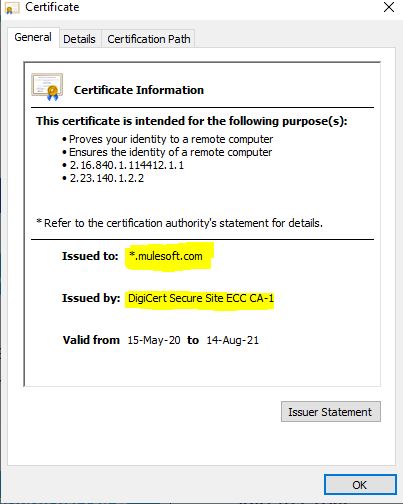
How our browser trusted MuleSoft site? If you click on the small lock on your browser address bar and then click on the certificate, you can see that this certificate is issued by DigiCert Secure Site ECC CA-1.
But, if you check in your browser Root CAs list, you won’t find this DigiCert Secure Site ECC CA-1 but still it is trusted? The reason is that this intermediate CA itself is trusted by Root CA DigiCert (DigiCert Global Root CA) which is a Certificate Authority with its certificate available in your trust store and hence completing this chain of trust.
I hope that this article will help you understand SSL basic concepts about how chain of trust works and how Root Certificate, Intermediate Certificates and Server (Leaf) certificates work in the SSL hand shake process to initiate a secure SSL/TLS connection between a client and server.

Pingback: An Overview of One-Way SSL and Two-Way SSL | TutorialsPedia
Pingback: SSL Certificate Concepts: How SSL/TLS Works: SSL/TLS Introduction | TutorialsPedia
Pingback: SSL vs TLS: What is the Difference Between SSL and TLS